This blog has been updated and may be updated in the future.
There are many ways to improve the security of our web applications. In this blog, we provide you with some of the most popular ones – have a read!
These days, web applications are getting breached left, right, and center – we mean, you’re reading a data breach search engine’s blog right now, aren’t you?
Indeed, data breaches are a really big problem. With that being said, though, it isn’t a problem that cannot be resolved – with just a couple of short steps, you will be on your way to web application security heaven!
Securing Code
First, have a look through your code – as developers, we often think that our code is and will always be as safe as possible, however, that’s not always the case: you might be surprised how many cyberattacks occur due to the code not being protected against basic SQL injection, Cross-site Scripting, or other attacks. And we’re serious! To avoid that happening to you:
- Familiarize yourself with the attacks directed at web applications such as SQL injection, Cross-site Scripting, RFI, LFI, etc.
- Make sure to write your code according to well-known standards, such as those belonging to OWASP.
- If possible, use a Web Application Firewall (WAF.) Check this blog for more details.
Access Rights & Backups
Once you are positive that your code is safe, be cautious with access rights, credentials, and backup storage. Avoid granting too many access rights to users that do not exactly need to know certain things. For example, avoid granting all access rights to a database to a user that only needs to read data (run SELECT queries), etc.
Be cautious with backing up data, too – if you backup data, make sure to test all of your backups to ensure that they always can be recovered because your system will – will – go down when you least expect it to, trust us. Also, you might want to avoid backing your data up every day if you don’t work on your web application all the time – backing up once or twice a week will do.
OSINT
Once you’ve secured your code, made sure that all of your access rights are properly in place, and thoroughly tested all of your backups, it may be time to keep an eye on OSINT tools as well. One of the main OSINT tools in this space will be a data breach search engine – data breach search engines usually help with a multitude of things:
- They help you secure your email addresses, usernames, IP addresses, or website.
- The data derived from data breach search engines doesn’t occupy any space on your server.
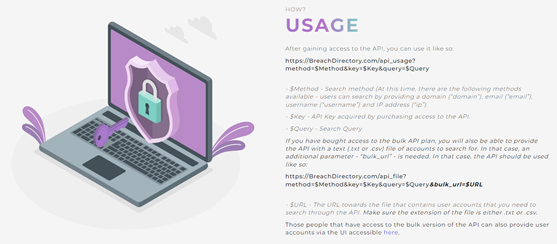
- Data breach search engines such as the one provided by BreachDirectory also have an API capability allowing you to sift through data and implement it into your own infrastructure.
- Most adequate data breach search engines come with a couple of plans: for example, the BreachDirectory API will let you associate the API with one system, multiple systems, resell the API keys, or query the data breach search engine for multiple accounts at once. Here’s what the BreachDirectory API documentation looks like:
Employing one or more of the aforementioned ways to protect your web applications will rapidly improve the security of your web applications. Make sure to employ at least a couple of these ways to protect yourself and your team, and until next time!